Hello there!
I am an engineer and physicist turned blockchain architect. I approach capital markets with a systems-view mindset: to build effective technology, you must first master the environment it operates in.
Currently, I lead digital asset product development at Nasdaq. Driven by a desire to understand the 'full stack' of our financial reality, my focus extends beyond the technology itself to the market structures it serves. By deconstructing the complex machinery of global finance, I apply my understanding of blockchain protocols to the areas where they offer genuine institutional value.
Recently Read
Read

Harvard Business Review Project Management Handbook: How to Launch, Lead, and Sponsor Successful Projects (HBR Handbooks)
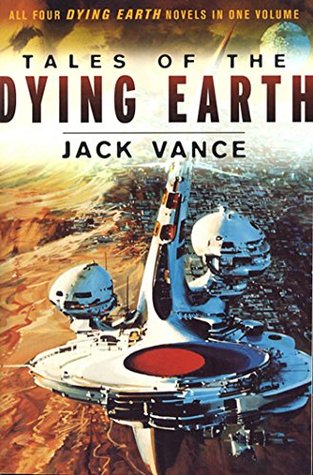
Tales of the Dying Earth: The Dying Earth, The Eyes of the Overworld, Cugel's Saga, Rhialto the Marvellous

Investing QuickStart Guide: The Simplified Beginner's Guide to Successfully Navigating the Stock Market, Growing Your Wealth & Creating a Secure Financial Future (QuickStart Guides™ - Finance)
Resume
Professional Experience
Leading Nasdaq's digital assets product strategy and development.
Manage an AWS cloud environment participating in a multi-party computation (MPC) signing infrastructure.
Oversee and coordinate deployments to production and UAT environments utilizing CI/CD practices (GitLab).
Conduct in-depth troubleshooting by analyzing Kubernetes pods in K9s, reviewing Grafana logs.
Responsible for the management of all digital assets on the Gemini exchange and segregated Custody product (>$30BN in May, 2021).
Operation and management of a fleet of Hardware Security Modules (HSMs). Coordinated and participated in key cloning ceremonies for HSMs.
Education
NSF Next Generation of Geospace Grant
Technical Skills
Projects
Personal Website
The source code for this website, built with Node.js.
Token Contract Viewer
A web app for deploying simulated token contracts and interacting with their ABIs.
Homelab
hover or click a unit to inspect // tap on mobile
Configuration Guides
▸ Global Ad-Blocking via Unraid, Pi-hole, and Tailscale 2026-04-04
Architecture Overview
This setup provides network-wide ad-blocking and custom DNS resolution to all roaming devices connected to a Tailscale mesh network.
The Design Choice: We use Host-Level Subnet Routing rather than a Tailscale Docker Sidecar.
Why: When assigning a Docker container a custom br0 (MACVLAN) IP on Unraid, Docker's virtual network adapter often fails to correctly route Tailscale's internal IPv6 MagicDNS traffic, causing infinite DNS loops or timeouts on Windows clients. Routing the tunnel directly through the Unraid host's native network stack bypasses this restriction entirely.
Phase 1: Unraid Host Preparation
- Navigate to your Unraid dashboard and go to Settings > Docker.
- Toggle Enable Docker to No and click Apply (you must stop the service to edit core settings).
- Switch the UI to Advanced View (toggle in the top right).
- Locate Host access to custom networks and change it to Enabled.
- Toggle Enable Docker back to Yes and click Apply.
Phase 2: Host-Level Tailscale Configuration
- Open the Unraid Terminal.
- Execute the Tailscale
upcommand, specifically appending the--advertise-routesflag for yourbr0subnet. - Command:
tailscale up --advertise-routes=10.0.10.2/232 - (Note: You can make this more permissive to include more IPs in the range using
/24if preferred, but/32covers just the single IP). Multiple single IPs can be advertised by using--advertise-routes=10.0.10.2/32,10.0.10.3/32
Phase 3: Pi-hole Docker Deployment
- In Unraid, go to the Docker tab and add/edit the Pi-hole container.
- Apply the following core network configurations:
- • Network Type:
Custom : br0 - • Fixed IP address:
10.0.10.2 - • Use Tailscale (Sidecar):
OFF - Ensure ports
53(TCP/UDP) and80(TCP) are mapped correctly. - Click Apply to build and start the container.
- Open the Pi-hole Web UI (
http://10.0.10.2/admin). (Note: You may need to set the password by opening a console to the container and runningpihole setpassword [PASSWORD]). - Go to Settings > DNS.
- Under Interface settings, select Permit all origins. (Required because queries will be arriving from
100.xTailscale IPs, not just the local10.0subnet). - Ensure your Upstream DNS Servers are set strictly to public providers (e.g., Cloudflare
1.1.1.1, Google8.8.8.8). Do not point upstream to your local router.
Phase 4: Tailscale Admin Console
- Log into the Tailscale Admin Console on the web.
- Approve the Route:
- • Go to the Machines tab and locate your Unraid server.
- • Click the three-dot menu and select Edit route settings.
- • Toggle the
10.0.10.2/32subnet route to ON. - Enforce Global DNS:
- • Navigate to the DNS tab.
- • Under Nameservers, click Add nameserver > Custom.
- • Enter the exact local IPv4 address of the Pi-hole:
10.0.10.2. - • Toggle Override local DNS to ON.
- • Ensure MagicDNS is enabled.
Phase 5: Client-Side Troubleshooting (Windows)
- If a Windows machine refuses to resolve hostnames after completing Phases 1-4:
- Flush the OS Cache:
- • Open an Administrator Command Prompt and run:
ipconfig /flushdns - • Check the DNS server you are using by running
nslookup - • Run
ipconfig /releaseandipconfig /renewto force the OS to pick up the new DNS settings. - • Restart the Tailscale client app.
Contact
Feel free to reach out through any of these platforms: